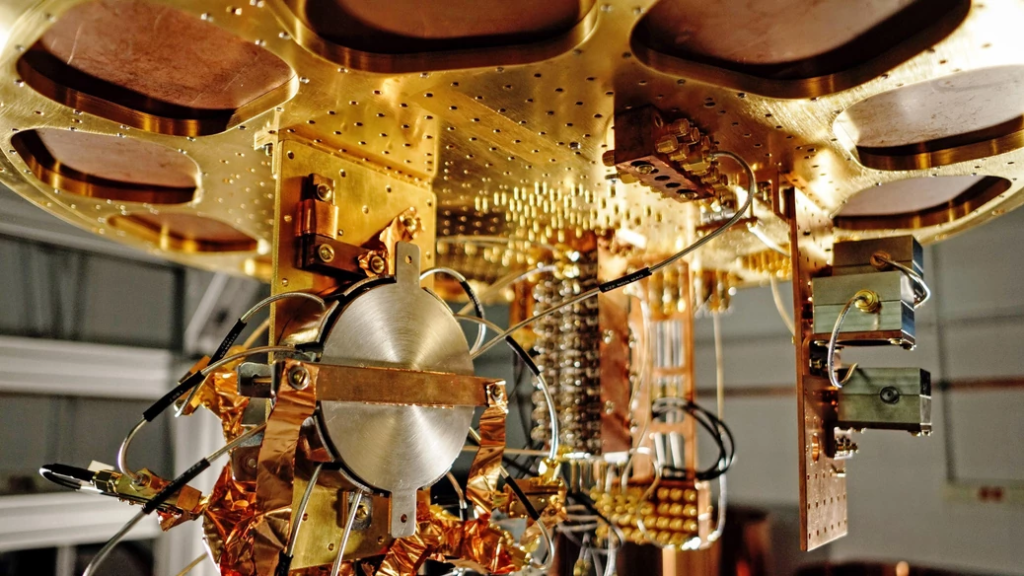
In today's increasingly digital world, the demand for secure and dependable cryptographic systems is at an all-time high. Blockchain technology has emerged as a revolutionary force in many industries, thanks to its decentralized and unchangeable characteristics. However, existing cryptographic algorithms face significant security threats from the advancing quantum computer technology. This article will discuss the significance of post-quantum cryptography in protecting blockchain networks against the impending quantum challenges.
Understanding the Quantum Threat
Quantum computers, employing quantum mechanics principles, promise unprecedented computational capabilities that may render existing cryptographic algorithms ineffective. Conventional encryption techniques, such as RSA and ECC (Elliptic Curve Cryptography), depend on the complexity of specific mathematical problems for security. Quantum computers, however, hold the potential to solve these problems exponentially faster, consequently dismantling the cryptographic foundation that supports blockchain networks.
Various risks are associated with quantum computers' impact on blockchain networks. The most prominent risk includes compromising the security of digital assets managed within blockchain systems. Transactions, smart contracts, and private keys that depend on cryptographic algorithms might become susceptible to quantum computer attacks. As quantum technology progresses, adversaries may decrypt encrypted information, tamper with transactions or counterfeit digital signatures – leading to severe financial and reputational damage for those relying on blockchain networks.
Additionally, blockchain's decentralized and transparent nature makes it particularly prone to quantum attacks. Given that blockchain transactions are publicly accessible, a quantum computer-equipped attacker could retroactively decrypt past transactions. This undermines the core principles of immutability and trust that underpin blockchain technology.
To address this urgent and critical challenge posed by the quantum threat, it's vital to take a proactive approach. Incorporating post-quantum cryptography into blockchain systems is crucial for maintaining long-term security and sustainability of these networks. By utilizing cryptographic algorithms that can withstand quantum computer attacks, blockchain networks can preserve data confidentiality, integrity, and the authenticity of transactions and digital assets. Even in light of quantum advancements.
The subsequent sections of this article will investigate the practicality of implementing post-quantum cryptography in blockchain systems. We will explore specific solutions, evaluate their performance implications, and emphasize the initiatives being taken towards standardization and compatibility. Through this examination, we seek to contribute to the comprehensive understanding and adoption of post-quantum cryptography as a vital defense against the quantum threat within the blockchain environment.
Read more about this topic!!
Exploring the Viability of Post-Quantum Cryptography in Blockchain
Implementing post-quantum cryptography within blockchain systems is a multifaceted effort demanding a thorough examination of numerous aspects. With the impending emergence of quantum computers, shifting to post-quantum cryptographic algorithms entails its own set of challenges. This section delves into the practicality of incorporating post-quantum cryptography into blockchain and scrutinizes the advancements in this domain.
Investigations and Progress in Algorithms
Intensive investigations are being undertaken by cryptographic researchers and organizations to explore post-quantum cryptographic algorithms that can withstand attacks from quantum computers. Lattice-based, code-based, and multivariate-based schemes are some examples that aim to preserve security even against quantum adversaries. Meticulous research and evaluations are performed to assess the mathematical underpinnings, security attributes, and practicality of these algorithms for actual implementation.
Concerns about Performance
A significant hurdle while adopting post-quantum cryptography in blockchain lies in the performance costs arising from these novel algorithms. Frequently, post-quantum cryptographic algorithms demand higher computational power and memory compared to conventional cryptographic algorithms. Such heightened computational requirements can influence blockchain networks' efficiency and scalability, possibly altering transaction throughput and consensus mechanisms. Nevertheless, ongoing investigations and optimization endeavors seek to address these performance issues, making post-quantum cryptography more practical for blockchain systems.
Integration with Current Blockchain Protocols
Modifications and revisions to existing protocols may be essential for integrating post-quantum cryptography into blockchain networks. Blockchain platforms like Ethereum proactively investigate incorporating post-quantum cryptographic algorithms through initiatives such as EIP-2938. The objectives include ensuring congruity and consensus among network users while establishing a trajectory towards quantum-resistant security.
The Role of Standardization and Interoperability
Standardization holds paramount importance when adopting and executing post-quantum cryptography within blockchain systems. Institutions like the National Institute of Standards and Technology have introduced competitions and evaluations to pinpoint and standardize post-quantum cryptographic algorithms. This standardization process confirms interoperability, cultivates trust, and facilitates widespread utilization of these algorithms across varied blockchain networks.
Test Implementations and Real-Life Evaluation
Multiple pilot projects and initiatives are launched to gauge the feasibility and practicability of p-q cryptography in actual blockchain settings. These implementations aid in pinpointing potential difficulties, performance consequences, and security considerations associated with merging post-quantum cryptography into existing blockchain infrastructures. The knowledge acquired from these pilot projects contributes to refining and enhancing post-quantum cryptographic algorithms for appropriateness within blockchain networks.
Evaluating Solutions for Post Quantum Cryptography Signature Verification
Hash-Based Signatures
Signature schemes based on hash functions, such as Lamport and Winternitz one-time signature schemes, provide post-quantum security due to the computational difficulty of hash functions. Although these schemes offer robust security assurances against quantum attacks, their large signature sizes make them less practical for bandwidth-restricted blockchain networks. Hash-based signatures are appropriate for situations where signature size is not a major concern, like in offline or low-bandwidth contexts.
Lattice-Based Signatures
BLISS and Dilithium schemes are examples of lattice-based signature schemes that leverage the difficulty of specific mathematical problems on lattices to ensure post-quantum security. These schemes have smaller signature sizes than hash-based signatures, rendering them more appropriate for resource-limited blockchain networks. Lattice-based signatures strike a good balance between security and efficiency; however, lattice operations' complexity can affect their performance.
Code-Based Signatures
Error-correcting codes are utilized in code-based signature schemes like McEliece and Niederreiter to provide quantum attack resistance. These schemes have small signature sizes and rapid signature generation capabilities, making them appealing for high-throughput blockchain systems. Nevertheless, code-based signatures may have larger public key sizes compared to other p-q cryptography signature schemes. This can influence storage requirements.
Multivariate-Based Signatures
Rainbow and HFE are multivariate-based signature schemes that rely on the difficulty of solving multivariate polynomial equation systems for post-quantum security. These schemes provide compact signature sizes and efficient signature verification, making them suitable for resource-limited blockchain networks. However, multivariate-based signatures can be prone to specific attacks, such as the Gröbner basis attack, necessitating cautious parameter selection and security analysis.
Hybrid Approaches
The integration of multiple post-quantum cryptography signature schemes characterizes hybrid approaches to capitalize on their respective benefits and address their shortcomings. A hybrid scheme can, for instance, merge a hash-based signature scheme for initial verification with a lattice-based or code-based signature scheme for additional validation. Hybrid approaches strive to deliver a sturdy and adaptable solution that harmonizes security, efficiency, and compatibility with existing cryptographic infrastructure.
When choosing a post-quantum cryptography signature verification solution for blockchain, it is critical to evaluate factors like security, signature size, computational efficiency, storage requirements, and protocol compatibility. The selection of a particular scheme will be determined by the blockchain network's specific demands and limitations.
It is important to note that it remains a developing field, with ongoing research and progress constantly enhancing signature schemes' efficiency and security. Keeping abreast of the latest developments and seeking advice from cryptographic experts is essential when making informed decisions regarding the adoption and implementation of it signature verification solutions in blockchain systems.
Blockchain developers and organizations can choose suitable post-quantum cryptography signature verification schemes by meticulously evaluating and comparing available options, ensuring robust defense against quantum attacks while maintaining optimal performance and scalability levels.
Moving Towards Standardization and Compatibility in Post-Quantum Cryptography:
The significance of standardization grows, enabling interoperability and compatibility among diverse blockchain networks. The adoption of post-quantum cryptographic algorithms and secure digital communication relies heavily on standardization. In this section, we will explore standardization's importance and the developments made thus far.
Standardization of Post-Quantum Cryptography by NIST
- The National Institute of Standards and Technology (NIST) is at the forefront of standardizing post-quantum cryptography.
- In 2017, NIST launched a public contest inviting submissions for post-quantum cryptography candidate algorithms across various categories, such as encryption, signature, and key exchange.
- This contest seeks to pinpoint and select quantum-resistant algorithms that are efficient, robust, and can be widely implemented across various applications and sectors.
- Currently in its final stages, the competition is narrowing down several algorithms for potential post-quantum cryptography standards.
Challenges in Interoperability and Compatibility:
- Attaining compatibility and interoperability among different cryptographic algorithms and blockchain networks is a complicated feat.
- Current blockchain systems often depend on specific cryptographic protocols and primitives that may not align with post-quantum algorithms.
- A seamless shift demands thorough examination of backward compatibility, migration strategies, and consensus from participants.
- Collaborative initiatives are essential for creating standards and protocols capable of smoothly integrating post-quantum cryptographic algorithms into existing blockchain networks.
Advantages of Standardization for Blockchain Networks:
- The adoption of post-quantum cryptography by blockchain networks brings numerous benefits through standardization.
- A common framework for cryptographic operations ensures interoperability, enabling secure communication among various blockchain platforms.
- Algorithms undergoing standardization are rigorously assessed by the cryptography community, instilling confidence in their reliability and security.
- Additionally, standardized frameworks simplify the integration of new cryptographic technologies and future enhancements.
Expanding Post-Quantum Cryptography to Additional Blockchain Networks:
The implementation of post-quantum cryptography spans beyond any single blockchain network or protocol. To guarantee long-term security and robustness of their systems, multiple blockchain platforms investigate ways to integrate post-quantum cryptographic algorithms as the quantum threat emerges. In this section, we will examine ongoing efforts to introduce post-quantum cryptography to other blockchain networks.
Ethereum and Post-Quantum Cryptography:
- As one of the most prevalent blockchain platforms, Ethereum actively investigates the adoption of post-quantum cryptographic algorithms.
- The Ethereum Foundation and its community engage in ongoing dialogue and partnerships with experts to evaluate the feasibility and appropriateness of various post-quantum algorithms for Ethereum's infrastructure.
- Developing a roadmap for incorporating post-quantum cryptography that considers the potential impact on performance, scalability, and backward compatibility is the ultimate goal.
Other Blockchain Networks:
- Outside of Ethereum, additional blockchain networks recognize the value of post-quantum cryptography.
- Platforms like Hyperledger, Corda, and Polkadot proactively explore how quantum-resistant algorithms can be integrated into their protocols to counter emerging threats.
- Collaborative work focuses on assessing and testing different post-quantum cryptographic solutions within real-world blockchain settings, taking into account factors such as performance, security, and infrastructure compatibility.
By expanding post-quantum cryptography to various blockchain networks, the goal is to construct a more secure and future-proof foundation for decentralized applications and digital asset transactions. Collaboration between standardization organizations, cryptographic experts, and blockchain platforms is vital in achieving
Conclusion
In conclusion, post-quantum cryptography offers a promising solution to address the quantum threat in blockchain. Efforts are underway to develop efficient and secure algorithms for post-quantum signature verification. Standardization and compatibility initiatives are crucial for seamless integration across different blockchain networks. The industry is actively working towards extending pq cryptography to ensure the security of blockchain transactions.
Looking for exceptional Web3 & Blockchain developers for your project? Contact us!
 en
en  pl
pl